Management VPC
Overview
This service contains code to deploy a Virtual Private Cloud (VPC) on AWS that can be used for administrative and management purposes, such as CI/CD services. The primary difference between this and the application VPC is this one has two subnet tiers (public and private) while the application VPC has three (public, private, and persistence). In this management VPC, we assume that there are no data stores that need to be separated in to a dedicated persistence tier.
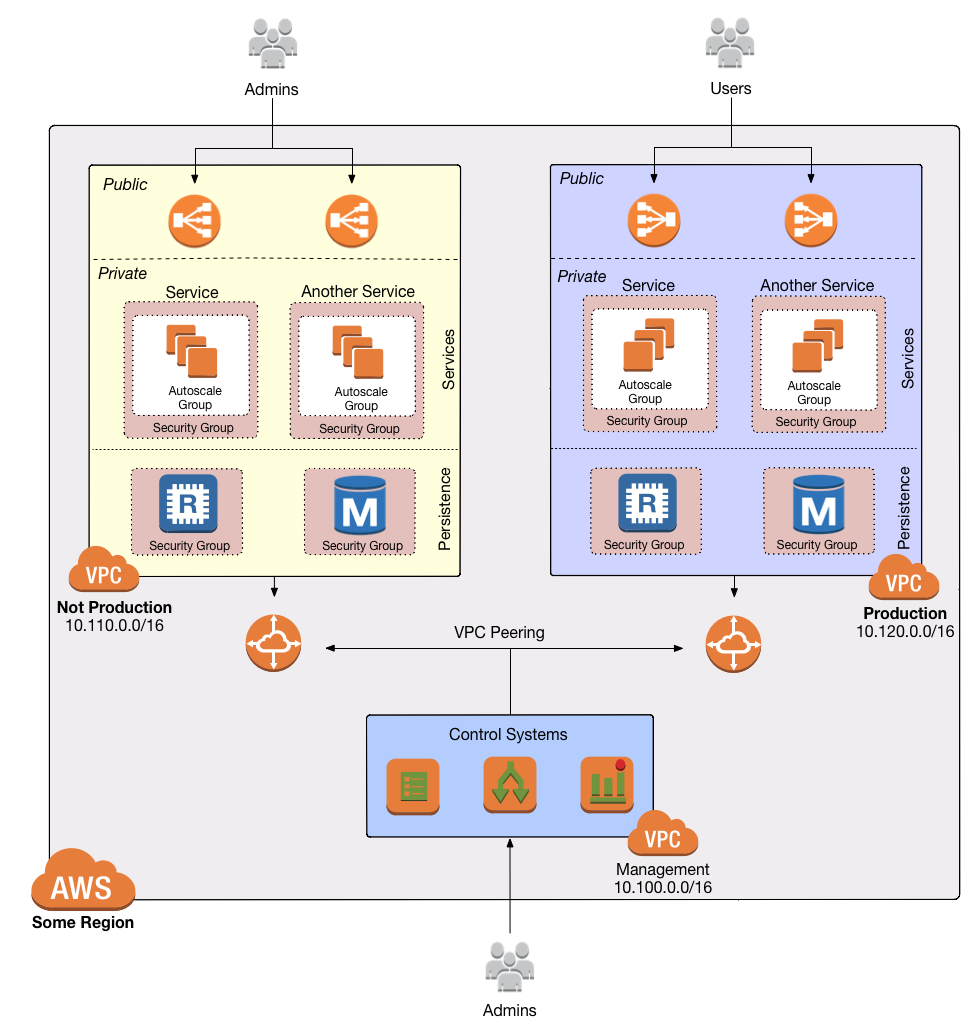 VPC architecture
VPC architecture
Features
- The VPC itself.
- Subnets, which are isolated subdivisions within the VPC. There are 2 "tiers" of subnets, public and private, spanning multiple availability zones.
- Route tables, which provide routing rules for the subnets.
- Internet Gateways to route traffic to the public Internet from public subnets.
- NATs to route traffic to the public Internet from private subnets.
Learn
This repo is a part of the Gruntwork Service Catalog, a collection of reusable, battle-tested, production ready infrastructure code. If you’ve never used the Service Catalog before, make sure to read How to use the Gruntwork Service Catalog!
Under the hood, this is all implemented using Terraform modules from the Gruntwork terraform-aws-vpc repo. If you are a subscriber and don’t have access to this repo, email support@gruntwork.io.
Core concepts
To understand core concepts like what’s a VPC, how subnets are configured, how network ACLs work, and more, see the documentation in the terraform-aws-vpc repo.
Repo organization
- modules: The main implementation code for this repo, broken down into multiple standalone, orthogonal submodules.
- examples: This folder contains working examples of how to use the submodules.
- test: Automated tests for the modules and examples.
Deploy
Non-production deployment (quick start for learning)
If you just want to try this repo out for experimenting and learning, check out the following resources:
- examples/for-learning-and-testing folder: The
examples/for-learning-and-testingfolder contains standalone sample code optimized for learning, experimenting, and testing (but not direct production usage).
Production deployment
If you want to deploy this repo in production, check out the following resources:
- examples/for-production folder: The
examples/for-productionfolder contains sample code optimized or direct usage in production. This is code from the Gruntwork Reference Architecture, and it shows you how we build an end-to-end, integrated tech stack on top of the Gruntwork Service Catalog. - How to deploy a production-grade VPC on AWS
- How to configure a production-grade CI/CD workflow for application and infrastructure code: step-by-step guide on how to configure CI / CD for your apps and infrastructure.
Sample Usage
- Terraform
- Terragrunt
# ------------------------------------------------------------------------------------------------------
# DEPLOY GRUNTWORK'S VPC-MGMT MODULE
# ------------------------------------------------------------------------------------------------------
module "vpc_mgmt" {
source = "git::git@github.com:gruntwork-io/terraform-aws-service-catalog.git//modules/networking/vpc-mgmt?ref=v0.126.3"
# ----------------------------------------------------------------------------------------------------
# REQUIRED VARIABLES
# ----------------------------------------------------------------------------------------------------
# The AWS region to deploy into
aws_region = <string>
# The IP address range of the VPC in CIDR notation. A prefix of /16 is
# recommended. Do not use a prefix higher than /27. Examples include
# '10.100.0.0/16', '10.200.0.0/16', etc.
cidr_block = <string>
# The number of NAT Gateways to launch for this VPC. The management VPC
# defaults to 1 NAT Gateway to save on cost, but to increase redundancy, you
# can adjust this to add additional NAT Gateways.
num_nat_gateways = <number>
# The name of the VPC. Defaults to mgmt.
vpc_name = <string>
# ----------------------------------------------------------------------------------------------------
# OPTIONAL VARIABLES
# ----------------------------------------------------------------------------------------------------
# If true, will apply the default NACL rules in var.default_nacl_ingress_rules
# and var.default_nacl_egress_rules on the default NACL of the VPC. Note that
# every VPC must have a default NACL - when this is false, the original
# default NACL rules managed by AWS will be used.
apply_default_nacl_rules = false
# If true, will associate the default NACL to the public, private, and
# persistence subnets created by this module. Only used if
# var.apply_default_nacl_rules is true. Note that this does not guarantee that
# the subnets are associated with the default NACL. Subnets can only be
# associated with a single NACL. The default NACL association will be dropped
# if the subnets are associated with a custom NACL later.
associate_default_nacl_to_subnets = true
# List of excluded Availability Zone IDs.
availability_zone_exclude_ids = []
# List of excluded Availability Zone names.
availability_zone_exclude_names = []
# Allows to filter list of Availability Zones based on their current state.
# Can be either "available", "information", "impaired" or "unavailable". By
# default the list includes a complete set of Availability Zones to which the
# underlying AWS account has access, regardless of their state.
availability_zone_state = null
# If you set this variable to false, this module will not create VPC Flow Logs
# resources. This is used as a workaround because Terraform does not allow you
# to use the 'count' parameter on modules. By using this parameter, you can
# optionally create or not create the resources within this module.
create_flow_logs = true
# If set to false, this module will NOT create Network ACLs. This is useful if
# you don't want to use Network ACLs or you want to provide your own Network
# ACLs outside of this module.
create_network_acls = true
# A map of tags to apply to the VPC, Subnets, Route Tables, and Internet
# Gateway. The key is the tag name and the value is the tag value. Note that
# the tag 'Name' is automatically added by this module but may be optionally
# overwritten by this variable.
custom_tags = {}
# A map of tags to apply just to the VPC itself, but not any of the other
# resources. The key is the tag name and the value is the tag value. Note that
# tags defined here will override tags defined as custom_tags in case of
# conflict.
custom_tags_vpc_only = {}
# The egress rules to apply to the default NACL in the VPC. This is the
# security group that is used by any subnet that doesn't have its own NACL
# attached. The value for this variable must be a map where the keys are a
# unique name for each rule and the values are objects with the same fields as
# the egress block in the aws_default_network_acl resource:
# https://registry.terraform.io/providers/hashicorp/aws/latest/docs/resources/default_network_acl.
default_nacl_egress_rules = {"AllowAll":{"action":"allow","cidr_block":"0.0.0.0/0","from_port":0,"protocol":"-1","rule_no":100,"to_port":0}}
# The ingress rules to apply to the default NACL in the VPC. This is the NACL
# that is used by any subnet that doesn't have its own NACL attached. The
# value for this variable must be a map where the keys are a unique name for
# each rule and the values are objects with the same fields as the ingress
# block in the aws_default_network_acl resource:
# https://registry.terraform.io/providers/hashicorp/aws/latest/docs/resources/default_network_acl.
default_nacl_ingress_rules = {"AllowAll":{"action":"allow","cidr_block":"0.0.0.0/0","from_port":0,"protocol":"-1","rule_no":100,"to_port":0}}
# The egress rules to apply to the default security group in the VPC. This is
# the security group that is used by any resource that doesn't have its own
# security group attached. The value for this variable must be a map where the
# keys are a unique name for each rule and the values are objects with the
# same fields as the egress block in the aws_default_security_group resource:
# https://registry.terraform.io/providers/hashicorp/aws/latest/docs/resources/default_security_group#egress-block.
default_security_group_egress_rules = {"AllowAllOutbound":{"cidr_blocks":["0.0.0.0/0"],"from_port":0,"ipv6_cidr_blocks":["::/0"],"protocol":"-1","to_port":0}}
# The ingress rules to apply to the default security group in the VPC. This is
# the security group that is used by any resource that doesn't have its own
# security group attached. The value for this variable must be a map where the
# keys are a unique name for each rule and the values are objects with the
# same fields as the ingress block in the aws_default_security_group resource:
# https://registry.terraform.io/providers/hashicorp/aws/latest/docs/resources/default_security_group#ingress-block.
default_security_group_ingress_rules = {"AllowAllFromSelf":{"from_port":0,"protocol":"-1","self":true,"to_port":0}}
# IAM policy to restrict what resources can call this endpoint. For example,
# you can add an IAM policy that allows EC2 instances to talk to this endpoint
# but no other types of resources. If not specified, all resources will be
# allowed to call this endpoint.
dynamodb_endpoint_policy = null
# If set to false, the default security groups will NOT be created.
enable_default_security_group = false
# Specifies the number of days you want to retain log events. Possible values
# are: 1, 3, 5, 7, 14, 30, 60, 90, 120, 150, 180, 365, 400, 545, 731, 1096,
# 1827, 2192, 2557, 2922, 3288, 3653, and 0. If you select 0, the events in
# the log group are always retained and never expire.
flow_log_cloudwatch_log_group_retention_in_days = 0
# The maximum interval of time during which a flow of packets is captured and
# aggregated into a flow log record. Valid values: 60 seconds (1 minute) or
# 600 seconds (10 minutes).
flow_log_max_aggregation_interval = 600
# The ARN of the policy that is used to set the permissions boundary for the
# IAM role.
iam_role_permissions_boundary = null
# The ARN of a KMS key to use for encrypting VPC the flow log. A new KMS key
# will be created if this is not supplied.
kms_key_arn = null
# The number of days to retain this KMS Key (a Customer Master Key) after it
# has been marked for deletion. Setting to null defaults to the provider
# default, which is the maximum possible value (30 days).
kms_key_deletion_window_in_days = null
# VPC Flow Logs will be encrypted with a KMS Key (a Customer Master Key). The
# IAM Users specified in this list will have access to this key.
kms_key_user_iam_arns = null
# A map of tags to apply to the NAT gateways, on top of the custom_tags. The
# key is the tag name and the value is the tag value. Note that tags defined
# here will override tags defined as custom_tags in case of conflict.
nat_gateway_custom_tags = {}
# How many AWS Availability Zones (AZs) to use. One subnet of each type
# (public, private app) will be created in each AZ. Note that this must be
# less than or equal to the total number of AZs in a region. A value of null
# means all AZs should be used. For example, if you specify 3 in a region with
# 5 AZs, subnets will be created in just 3 AZs instead of all 5. Defaults to
# 3.
num_availability_zones = null
# Takes the CIDR prefix and adds these many bits to it for calculating subnet
# ranges. MAKE SURE if you change this you also change the CIDR spacing or
# you may hit errors. See cidrsubnet interpolation in terraform config for
# more information.
private_subnet_bits = 4
# A map listing the specific CIDR blocks desired for each private subnet. The
# key must be in the form AZ-0, AZ-1, ... AZ-n where n is the number of
# Availability Zones. If left blank, we will compute a reasonable CIDR block
# for each subnet.
private_subnet_cidr_blocks = {}
# A map of tags to apply to the private Subnet, on top of the custom_tags. The
# key is the tag name and the value is the tag value. Note that tags defined
# here will override tags defined as custom_tags in case of conflict.
private_subnet_custom_tags = {}
# Takes the CIDR prefix and adds these many bits to it for calculating subnet
# ranges. MAKE SURE if you change this you also change the CIDR spacing or
# you may hit errors. See cidrsubnet interpolation in terraform config for
# more information.
public_subnet_bits = 4
# A map listing the specific CIDR blocks desired for each public subnet. The
# key must be in the form AZ-0, AZ-1, ... AZ-n where n is the number of
# Availability Zones. If left blank, we will compute a reasonable CIDR block
# for each subnet.
public_subnet_cidr_blocks = {}
# A map of tags to apply to the public Subnet, on top of the custom_tags. The
# key is the tag name and the value is the tag value. Note that tags defined
# here will override tags defined as custom_tags in case of conflict.
public_subnet_custom_tags = {}
# IAM policy to restrict what resources can call this endpoint. For example,
# you can add an IAM policy that allows EC2 instances to talk to this endpoint
# but no other types of resources. If not specified, all resources will be
# allowed to call this endpoint.
s3_endpoint_policy = null
# The amount of spacing between the different subnet types
subnet_spacing = 8
# When true, all IAM policies will be managed as dedicated policies rather
# than inline policies attached to the IAM roles. Dedicated managed policies
# are friendlier to automated policy checkers, which may scan a single
# resource for findings. As such, it is important to avoid inline policies
# when targeting compliance with various security standards.
use_managed_iam_policies = true
}
# ------------------------------------------------------------------------------------------------------
# DEPLOY GRUNTWORK'S VPC-MGMT MODULE
# ------------------------------------------------------------------------------------------------------
terraform {
source = "git::git@github.com:gruntwork-io/terraform-aws-service-catalog.git//modules/networking/vpc-mgmt?ref=v0.126.3"
}
inputs = {
# ----------------------------------------------------------------------------------------------------
# REQUIRED VARIABLES
# ----------------------------------------------------------------------------------------------------
# The AWS region to deploy into
aws_region = <string>
# The IP address range of the VPC in CIDR notation. A prefix of /16 is
# recommended. Do not use a prefix higher than /27. Examples include
# '10.100.0.0/16', '10.200.0.0/16', etc.
cidr_block = <string>
# The number of NAT Gateways to launch for this VPC. The management VPC
# defaults to 1 NAT Gateway to save on cost, but to increase redundancy, you
# can adjust this to add additional NAT Gateways.
num_nat_gateways = <number>
# The name of the VPC. Defaults to mgmt.
vpc_name = <string>
# ----------------------------------------------------------------------------------------------------
# OPTIONAL VARIABLES
# ----------------------------------------------------------------------------------------------------
# If true, will apply the default NACL rules in var.default_nacl_ingress_rules
# and var.default_nacl_egress_rules on the default NACL of the VPC. Note that
# every VPC must have a default NACL - when this is false, the original
# default NACL rules managed by AWS will be used.
apply_default_nacl_rules = false
# If true, will associate the default NACL to the public, private, and
# persistence subnets created by this module. Only used if
# var.apply_default_nacl_rules is true. Note that this does not guarantee that
# the subnets are associated with the default NACL. Subnets can only be
# associated with a single NACL. The default NACL association will be dropped
# if the subnets are associated with a custom NACL later.
associate_default_nacl_to_subnets = true
# List of excluded Availability Zone IDs.
availability_zone_exclude_ids = []
# List of excluded Availability Zone names.
availability_zone_exclude_names = []
# Allows to filter list of Availability Zones based on their current state.
# Can be either "available", "information", "impaired" or "unavailable". By
# default the list includes a complete set of Availability Zones to which the
# underlying AWS account has access, regardless of their state.
availability_zone_state = null
# If you set this variable to false, this module will not create VPC Flow Logs
# resources. This is used as a workaround because Terraform does not allow you
# to use the 'count' parameter on modules. By using this parameter, you can
# optionally create or not create the resources within this module.
create_flow_logs = true
# If set to false, this module will NOT create Network ACLs. This is useful if
# you don't want to use Network ACLs or you want to provide your own Network
# ACLs outside of this module.
create_network_acls = true
# A map of tags to apply to the VPC, Subnets, Route Tables, and Internet
# Gateway. The key is the tag name and the value is the tag value. Note that
# the tag 'Name' is automatically added by this module but may be optionally
# overwritten by this variable.
custom_tags = {}
# A map of tags to apply just to the VPC itself, but not any of the other
# resources. The key is the tag name and the value is the tag value. Note that
# tags defined here will override tags defined as custom_tags in case of
# conflict.
custom_tags_vpc_only = {}
# The egress rules to apply to the default NACL in the VPC. This is the
# security group that is used by any subnet that doesn't have its own NACL
# attached. The value for this variable must be a map where the keys are a
# unique name for each rule and the values are objects with the same fields as
# the egress block in the aws_default_network_acl resource:
# https://registry.terraform.io/providers/hashicorp/aws/latest/docs/resources/default_network_acl.
default_nacl_egress_rules = {"AllowAll":{"action":"allow","cidr_block":"0.0.0.0/0","from_port":0,"protocol":"-1","rule_no":100,"to_port":0}}
# The ingress rules to apply to the default NACL in the VPC. This is the NACL
# that is used by any subnet that doesn't have its own NACL attached. The
# value for this variable must be a map where the keys are a unique name for
# each rule and the values are objects with the same fields as the ingress
# block in the aws_default_network_acl resource:
# https://registry.terraform.io/providers/hashicorp/aws/latest/docs/resources/default_network_acl.
default_nacl_ingress_rules = {"AllowAll":{"action":"allow","cidr_block":"0.0.0.0/0","from_port":0,"protocol":"-1","rule_no":100,"to_port":0}}
# The egress rules to apply to the default security group in the VPC. This is
# the security group that is used by any resource that doesn't have its own
# security group attached. The value for this variable must be a map where the
# keys are a unique name for each rule and the values are objects with the
# same fields as the egress block in the aws_default_security_group resource:
# https://registry.terraform.io/providers/hashicorp/aws/latest/docs/resources/default_security_group#egress-block.
default_security_group_egress_rules = {"AllowAllOutbound":{"cidr_blocks":["0.0.0.0/0"],"from_port":0,"ipv6_cidr_blocks":["::/0"],"protocol":"-1","to_port":0}}
# The ingress rules to apply to the default security group in the VPC. This is
# the security group that is used by any resource that doesn't have its own
# security group attached. The value for this variable must be a map where the
# keys are a unique name for each rule and the values are objects with the
# same fields as the ingress block in the aws_default_security_group resource:
# https://registry.terraform.io/providers/hashicorp/aws/latest/docs/resources/default_security_group#ingress-block.
default_security_group_ingress_rules = {"AllowAllFromSelf":{"from_port":0,"protocol":"-1","self":true,"to_port":0}}
# IAM policy to restrict what resources can call this endpoint. For example,
# you can add an IAM policy that allows EC2 instances to talk to this endpoint
# but no other types of resources. If not specified, all resources will be
# allowed to call this endpoint.
dynamodb_endpoint_policy = null
# If set to false, the default security groups will NOT be created.
enable_default_security_group = false
# Specifies the number of days you want to retain log events. Possible values
# are: 1, 3, 5, 7, 14, 30, 60, 90, 120, 150, 180, 365, 400, 545, 731, 1096,
# 1827, 2192, 2557, 2922, 3288, 3653, and 0. If you select 0, the events in
# the log group are always retained and never expire.
flow_log_cloudwatch_log_group_retention_in_days = 0
# The maximum interval of time during which a flow of packets is captured and
# aggregated into a flow log record. Valid values: 60 seconds (1 minute) or
# 600 seconds (10 minutes).
flow_log_max_aggregation_interval = 600
# The ARN of the policy that is used to set the permissions boundary for the
# IAM role.
iam_role_permissions_boundary = null
# The ARN of a KMS key to use for encrypting VPC the flow log. A new KMS key
# will be created if this is not supplied.
kms_key_arn = null
# The number of days to retain this KMS Key (a Customer Master Key) after it
# has been marked for deletion. Setting to null defaults to the provider
# default, which is the maximum possible value (30 days).
kms_key_deletion_window_in_days = null
# VPC Flow Logs will be encrypted with a KMS Key (a Customer Master Key). The
# IAM Users specified in this list will have access to this key.
kms_key_user_iam_arns = null
# A map of tags to apply to the NAT gateways, on top of the custom_tags. The
# key is the tag name and the value is the tag value. Note that tags defined
# here will override tags defined as custom_tags in case of conflict.
nat_gateway_custom_tags = {}
# How many AWS Availability Zones (AZs) to use. One subnet of each type
# (public, private app) will be created in each AZ. Note that this must be
# less than or equal to the total number of AZs in a region. A value of null
# means all AZs should be used. For example, if you specify 3 in a region with
# 5 AZs, subnets will be created in just 3 AZs instead of all 5. Defaults to
# 3.
num_availability_zones = null
# Takes the CIDR prefix and adds these many bits to it for calculating subnet
# ranges. MAKE SURE if you change this you also change the CIDR spacing or
# you may hit errors. See cidrsubnet interpolation in terraform config for
# more information.
private_subnet_bits = 4
# A map listing the specific CIDR blocks desired for each private subnet. The
# key must be in the form AZ-0, AZ-1, ... AZ-n where n is the number of
# Availability Zones. If left blank, we will compute a reasonable CIDR block
# for each subnet.
private_subnet_cidr_blocks = {}
# A map of tags to apply to the private Subnet, on top of the custom_tags. The
# key is the tag name and the value is the tag value. Note that tags defined
# here will override tags defined as custom_tags in case of conflict.
private_subnet_custom_tags = {}
# Takes the CIDR prefix and adds these many bits to it for calculating subnet
# ranges. MAKE SURE if you change this you also change the CIDR spacing or
# you may hit errors. See cidrsubnet interpolation in terraform config for
# more information.
public_subnet_bits = 4
# A map listing the specific CIDR blocks desired for each public subnet. The
# key must be in the form AZ-0, AZ-1, ... AZ-n where n is the number of
# Availability Zones. If left blank, we will compute a reasonable CIDR block
# for each subnet.
public_subnet_cidr_blocks = {}
# A map of tags to apply to the public Subnet, on top of the custom_tags. The
# key is the tag name and the value is the tag value. Note that tags defined
# here will override tags defined as custom_tags in case of conflict.
public_subnet_custom_tags = {}
# IAM policy to restrict what resources can call this endpoint. For example,
# you can add an IAM policy that allows EC2 instances to talk to this endpoint
# but no other types of resources. If not specified, all resources will be
# allowed to call this endpoint.
s3_endpoint_policy = null
# The amount of spacing between the different subnet types
subnet_spacing = 8
# When true, all IAM policies will be managed as dedicated policies rather
# than inline policies attached to the IAM roles. Dedicated managed policies
# are friendlier to automated policy checkers, which may scan a single
# resource for findings. As such, it is important to avoid inline policies
# when targeting compliance with various security standards.
use_managed_iam_policies = true
}
Reference
- Inputs
- Outputs
Required
aws_regionstringThe AWS region to deploy into
cidr_blockstringThe IP address range of the VPC in CIDR notation. A prefix of /16 is recommended. Do not use a prefix higher than /27. Examples include '10.100.0.0/16', '10.200.0.0/16', etc.
num_nat_gatewaysnumberThe number of NAT Gateways to launch for this VPC. The management VPC defaults to 1 NAT Gateway to save on cost, but to increase redundancy, you can adjust this to add additional NAT Gateways.
vpc_namestringThe name of the VPC. Defaults to mgmt.
Optional
If true, will apply the default NACL rules in default_nacl_ingress_rules and default_nacl_egress_rules on the default NACL of the VPC. Note that every VPC must have a default NACL - when this is false, the original default NACL rules managed by AWS will be used.
falseIf true, will associate the default NACL to the public, private, and persistence subnets created by this module. Only used if apply_default_nacl_rules is true. Note that this does not guarantee that the subnets are associated with the default NACL. Subnets can only be associated with a single NACL. The default NACL association will be dropped if the subnets are associated with a custom NACL later.
trueavailability_zone_exclude_idslist(string)List of excluded Availability Zone IDs.
[]availability_zone_exclude_nameslist(string)List of excluded Availability Zone names.
[]availability_zone_statestringAllows to filter list of Availability Zones based on their current state. Can be either 'available', 'information', 'impaired' or 'unavailable'. By default the list includes a complete set of Availability Zones to which the underlying AWS account has access, regardless of their state.
nullcreate_flow_logsboolIf you set this variable to false, this module will not create VPC Flow Logs resources. This is used as a workaround because Terraform does not allow you to use the 'count' parameter on modules. By using this parameter, you can optionally create or not create the resources within this module.
trueIf set to false, this module will NOT create Network ACLs. This is useful if you don't want to use Network ACLs or you want to provide your own Network ACLs outside of this module.
truecustom_tagsmap(string)A map of tags to apply to the VPC, Subnets, Route Tables, and Internet Gateway. The key is the tag name and the value is the tag value. Note that the tag 'Name' is automatically added by this module but may be optionally overwritten by this variable.
{}custom_tags_vpc_onlymap(string)A map of tags to apply just to the VPC itself, but not any of the other resources. The key is the tag name and the value is the tag value. Note that tags defined here will override tags defined as custom_tags in case of conflict.
{}The egress rules to apply to the default NACL in the VPC. This is the security group that is used by any subnet that doesn't have its own NACL attached. The value for this variable must be a map where the keys are a unique name for each rule and the values are objects with the same fields as the egress block in the aws_default_network_acl resource: https://registry.terraform.io/providers/hashicorp/aws/latest/docs/resources/default_network_acl.
Any types represent complex values of variable type. For details, please consult `variables.tf` in the source repo.
{
AllowAll = {
action = "allow",
cidr_block = "0.0.0.0/0",
from_port = 0,
protocol = "-1",
rule_no = 100,
to_port = 0
}
}
The ingress rules to apply to the default NACL in the VPC. This is the NACL that is used by any subnet that doesn't have its own NACL attached. The value for this variable must be a map where the keys are a unique name for each rule and the values are objects with the same fields as the ingress block in the aws_default_network_acl resource: https://registry.terraform.io/providers/hashicorp/aws/latest/docs/resources/default_network_acl.
Any types represent complex values of variable type. For details, please consult `variables.tf` in the source repo.
{
AllowAll = {
action = "allow",
cidr_block = "0.0.0.0/0",
from_port = 0,
protocol = "-1",
rule_no = 100,
to_port = 0
}
}
The egress rules to apply to the default security group in the VPC. This is the security group that is used by any resource that doesn't have its own security group attached. The value for this variable must be a map where the keys are a unique name for each rule and the values are objects with the same fields as the egress block in the aws_default_security_group resource: https://registry.terraform.io/providers/hashicorp/aws/latest/docs/resources/default_security_group#egress-block.
Any types represent complex values of variable type. For details, please consult `variables.tf` in the source repo.
{
AllowAllOutbound = {
cidr_blocks = [
"0.0.0.0/0"
],
from_port = 0,
ipv6_cidr_blocks = [
"::/0"
],
protocol = "-1",
to_port = 0
}
}
The ingress rules to apply to the default security group in the VPC. This is the security group that is used by any resource that doesn't have its own security group attached. The value for this variable must be a map where the keys are a unique name for each rule and the values are objects with the same fields as the ingress block in the aws_default_security_group resource: https://registry.terraform.io/providers/hashicorp/aws/latest/docs/resources/default_security_group#ingress-block.
Any types represent complex values of variable type. For details, please consult `variables.tf` in the source repo.
{
AllowAllFromSelf = {
from_port = 0,
protocol = "-1",
self = true,
to_port = 0
}
}
dynamodb_endpoint_policystringIAM policy to restrict what resources can call this endpoint. For example, you can add an IAM policy that allows EC2 instances to talk to this endpoint but no other types of resources. If not specified, all resources will be allowed to call this endpoint.
nullIf set to false, the default security groups will NOT be created.
falseSpecifies the number of days you want to retain log events. Possible values are: 1, 3, 5, 7, 14, 30, 60, 90, 120, 150, 180, 365, 400, 545, 731, 1096, 1827, 2192, 2557, 2922, 3288, 3653, and 0. If you select 0, the events in the log group are always retained and never expire.
0The maximum interval of time during which a flow of packets is captured and aggregated into a flow log record. Valid values: 60 seconds (1 minute) or 600 seconds (10 minutes).
600The ARN of the policy that is used to set the permissions boundary for the IAM role.
nullkms_key_arnstringThe ARN of a KMS key to use for encrypting VPC the flow log. A new KMS key will be created if this is not supplied.
nullThe number of days to retain this KMS Key (a Customer Master Key) after it has been marked for deletion. Setting to null defaults to the provider default, which is the maximum possible value (30 days).
nullkms_key_user_iam_arnslist(string)VPC Flow Logs will be encrypted with a KMS Key (a Customer Master Key). The IAM Users specified in this list will have access to this key.
nullnat_gateway_custom_tagsmap(string)A map of tags to apply to the NAT gateways, on top of the custom_tags. The key is the tag name and the value is the tag value. Note that tags defined here will override tags defined as custom_tags in case of conflict.
{}num_availability_zonesnumberHow many AWS Availability Zones (AZs) to use. One subnet of each type (public, private app) will be created in each AZ. Note that this must be less than or equal to the total number of AZs in a region. A value of null means all AZs should be used. For example, if you specify 3 in a region with 5 AZs, subnets will be created in just 3 AZs instead of all 5. Defaults to 3.
nullprivate_subnet_bitsnumberTakes the CIDR prefix and adds these many bits to it for calculating subnet ranges. MAKE SURE if you change this you also change the CIDR spacing or you may hit errors. See cidrsubnet interpolation in terraform config for more information.
4private_subnet_cidr_blocksmap(string)A map listing the specific CIDR blocks desired for each private subnet. The key must be in the form AZ-0, AZ-1, ... AZ-n where n is the number of Availability Zones. If left blank, we will compute a reasonable CIDR block for each subnet.
{}private_subnet_custom_tagsmap(string)A map of tags to apply to the private Subnet, on top of the custom_tags. The key is the tag name and the value is the tag value. Note that tags defined here will override tags defined as custom_tags in case of conflict.
{}public_subnet_bitsnumberTakes the CIDR prefix and adds these many bits to it for calculating subnet ranges. MAKE SURE if you change this you also change the CIDR spacing or you may hit errors. See cidrsubnet interpolation in terraform config for more information.
4public_subnet_cidr_blocksmap(string)A map listing the specific CIDR blocks desired for each public subnet. The key must be in the form AZ-0, AZ-1, ... AZ-n where n is the number of Availability Zones. If left blank, we will compute a reasonable CIDR block for each subnet.
{}public_subnet_custom_tagsmap(string)A map of tags to apply to the public Subnet, on top of the custom_tags. The key is the tag name and the value is the tag value. Note that tags defined here will override tags defined as custom_tags in case of conflict.
{}s3_endpoint_policystringIAM policy to restrict what resources can call this endpoint. For example, you can add an IAM policy that allows EC2 instances to talk to this endpoint but no other types of resources. If not specified, all resources will be allowed to call this endpoint.
nullsubnet_spacingnumberThe amount of spacing between the different subnet types
8When true, all IAM policies will be managed as dedicated policies rather than inline policies attached to the IAM roles. Dedicated managed policies are friendlier to automated policy checkers, which may scan a single resource for findings. As such, it is important to avoid inline policies when targeting compliance with various security standards.
trueThe public IP address(es) of the NAT gateway(s) of the mgmt VPC.
The number of availability zones used by the mgmt VPC.
The private subnet ARNs of the mgmt VPC.
The private subnet CIDR blocks of the mgmt VPC.
The private subnet IDs of the mgmt VPC.
The ID of the private subnet route table of the mgmt VPC.
The public subnet ARNs of the mgmt VPC.
The public subnet CIDR blocks of the mgmt VPC.
The public subnet IDs of the mgmt VPC.
The ID of the public subnet route table of the mgmt VPC.
The CIDR block of the mgmt VPC.
The ID of the mgmt VPC.
The name of the mgmt VPC.
Indicates whether or not the VPC has finished creating